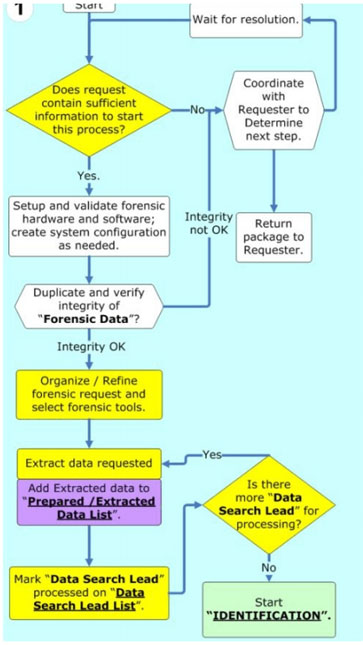
Generic Computer Forensic Investigation Model (GCFIM) Phase 1 of GCFIM... | Download Scientific Diagram
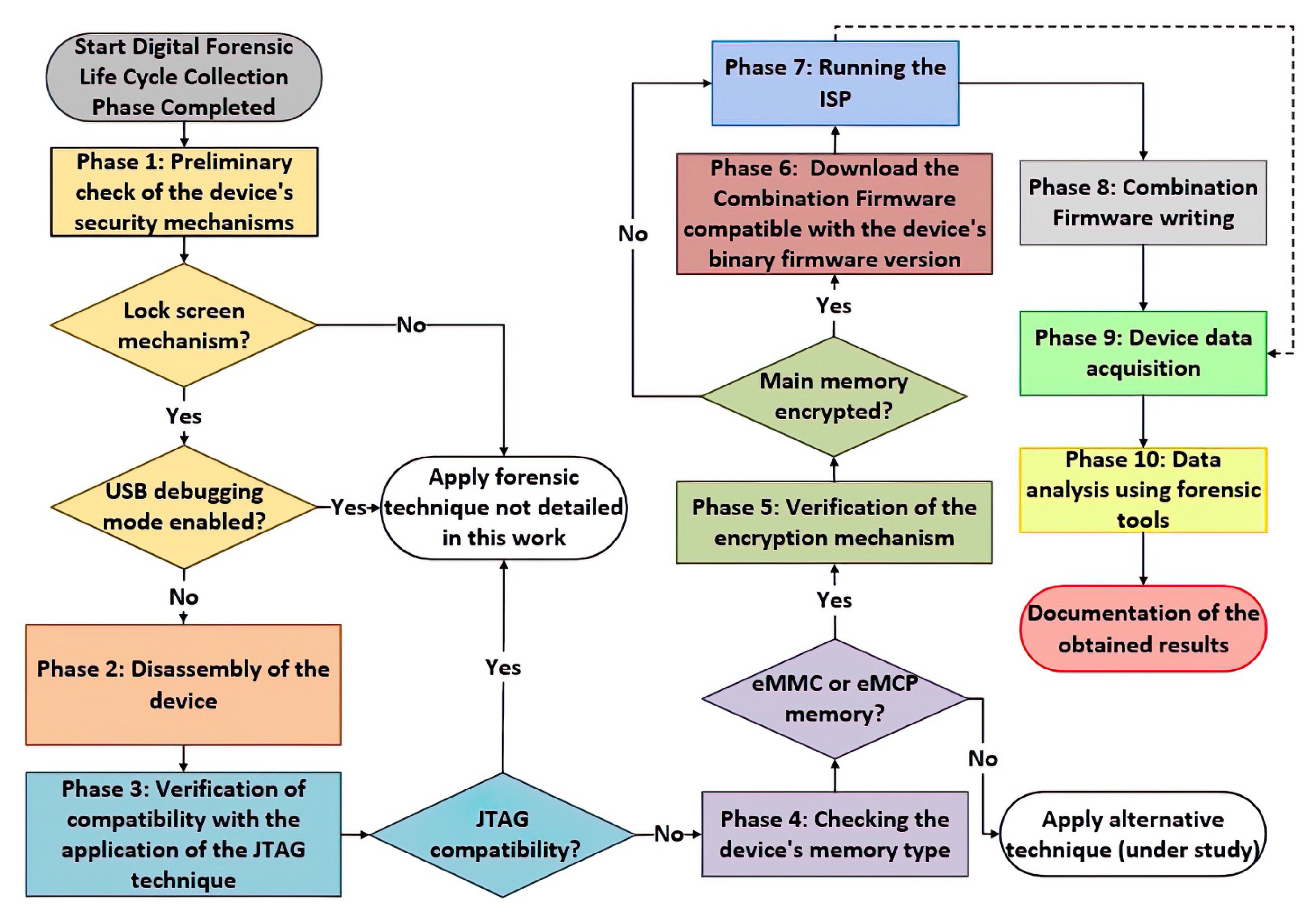
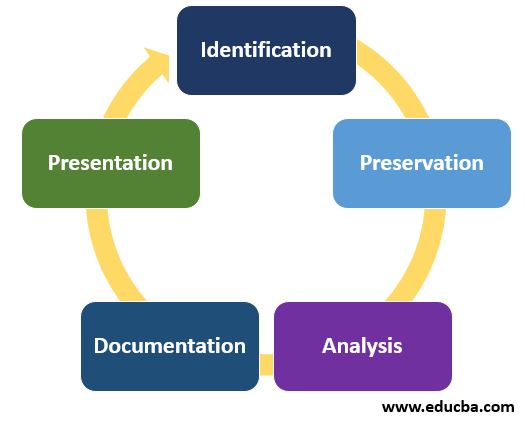
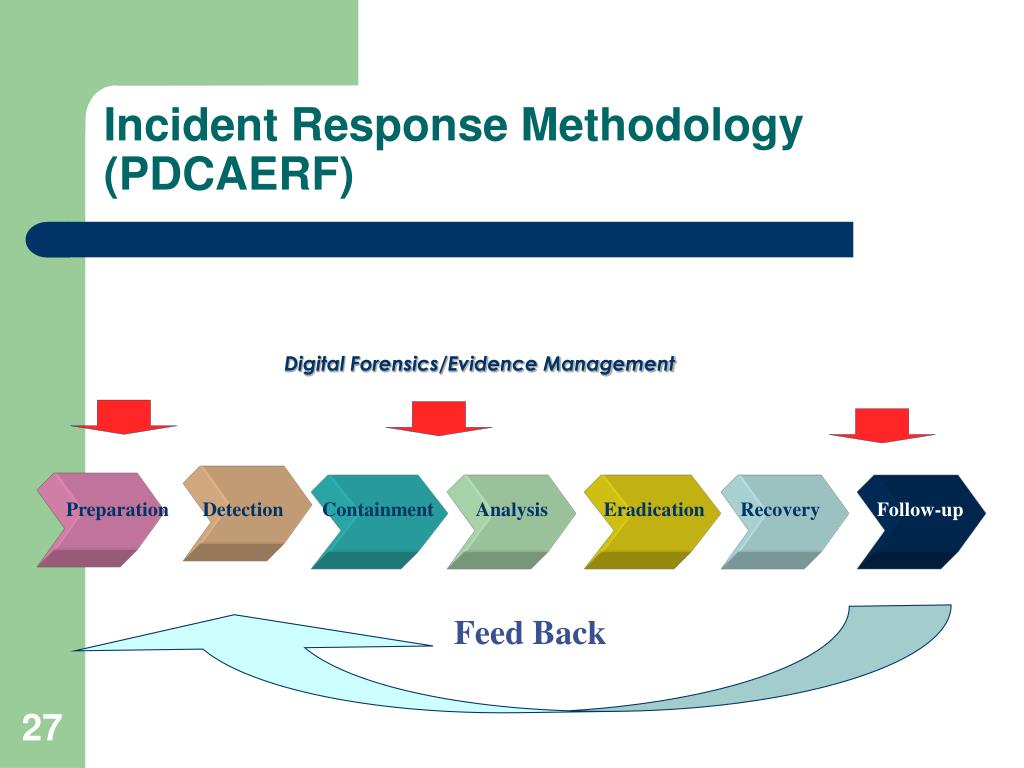
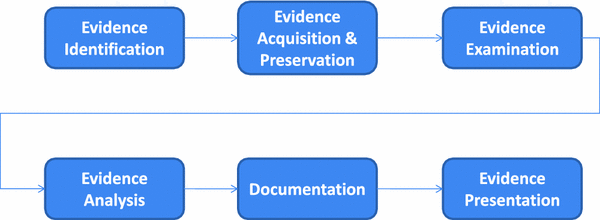
Applied Sciences | Free Full-Text | Methodology for Forensics Data Reconstruction on Mobile Devices with Android Operating System Applying In-System Programming and Combination Firmware | HTML

Generic Computer Forensic Investigation Model (GCFIM) Phase 1 of GCFIM... | Download Scientific Diagram